Are New Zealand's sub sea cables a cybersecurity risk?
Thu, 24th Feb 2022
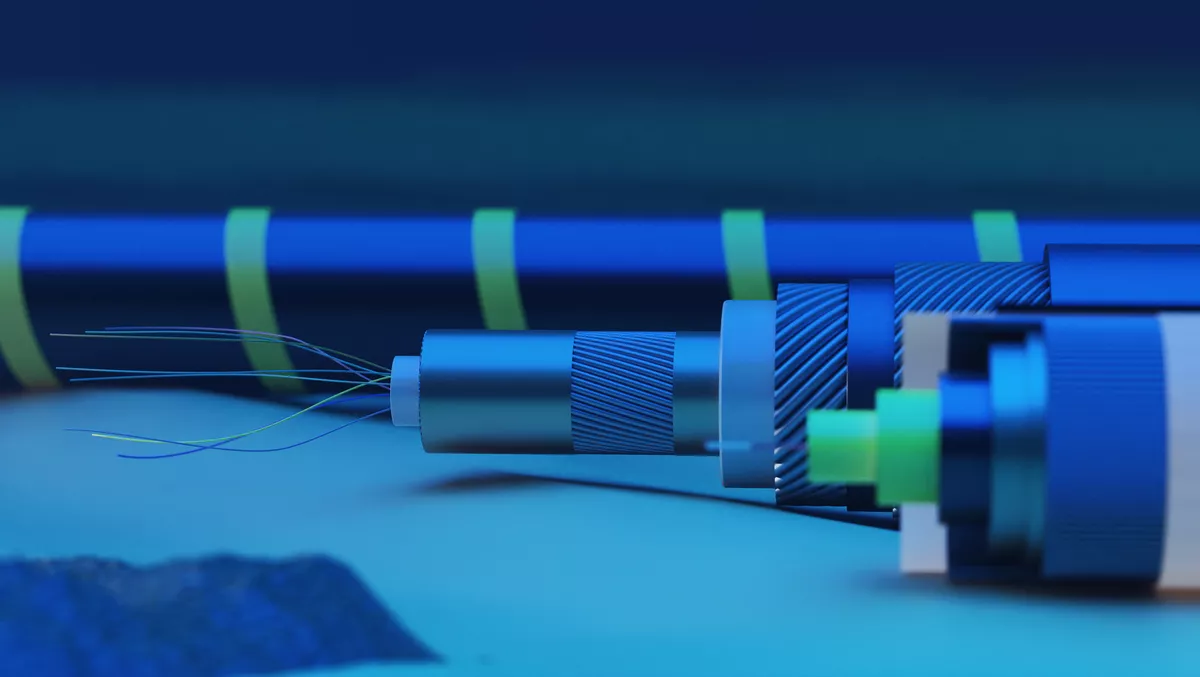
Submarine cable networks are often perceived as quite an anomaly to some. While they are generally a crucial part of a country's data and communication infrastructure, there is limited knowledge and public perception of the actual technology behind them, particularly from a security standpoint.
Recently, New Zealanders may have seen a fair bit in the press about cables, either concerning rapid reconnection in Tonga or the raft of new cable networks from New Zealand to across the globe.
The eruption in Tonga highlighted that cable security isn't just down to making sure digital security is up to date, but also the physical network infrastructure.
The demand for secure infrastructure of this type is rising, particularly with increased demands caused by the COVID-19 pandemic. NZ consumers are working more in hybrid environments and require robust connectivity and security for communication across the globe, often on the go and in a variety of network critical environments.
Data Centers are also a crucial aspect of the cable space, as having strongly connected data centers can increase stability and security. Ensuring these systems are secure and reliable is paramount to determining whether a cable connection works to its best capacity.
New Zealand is currently undergoing a substantial period of growth in the areas, with new innovations and opportunities arising constantly. However, with this increased uptake also comes increased risk.
Currently, there are four main submarine cable networks in NZ. These are the the Southern Cross Cable Network (SCCN), the Tasman Global Access (TGA), Hawaiki Cable and Aqualink. In 2013, it was reported that the owners of the Southern Cross cable had asked the United States National Security Agency to pay them for surveillance of New Zealanders internet activity through the cable network. This highlighted the real danger and privacy risks cables could cause in NZ, and although these allegations were denied it still made people think twice about how safe their cable networks are.
Hawaiki Submarine Cable LP is a name that many may have seen in the media lately, due to their new cable and data center projects. Headed by Remi Galasso, the company first launched its first commercial service in NZ in July 2018 with the Hawaiki Transpacific Cable. This behemoth cable provides connectivity between New Zealand, Australia and the United States, spanning 15,000km.
"International submarine cables remain the most critical of telecommunications infrastructure assets, providing essential connectivity linking countries to the rest of the world," says Galasso.
"Many people may not be aware that today, the vast majority (99.8%) of internet traffic traverses subsea cable systems, rather than satellite, as is commonly thought."
With so much reliance on cable networks, NZ consumers might be interested to know exactly how safe these new cables are and what processes are in place to keep them safe. If a cable is disrupted, data gets lost and if receiving technology and data centers aren't secure, then a plethora of issues can arise.
"Of course, satellites play a vital role given they can connect people anywhere on the planet. But they have limitations, including not being able to support the sorts of massive and growing volumes of traffic carried by subsea cables. As such, the two technologies have become extremely complementary in meeting today's connectivity challenges," says Galasso.
So how can New Zealanders be assured that their cable connections are secure? And what kinds of things do Hawaiki do to ensure the security of all NZ connections?
"Safety and security are front of mind from inception. From before actual construction, through to manufacturing and eventually installation, we follow strict processes involving multiple steps," Galasso says when speaking of Hawaiki's cable networks.
On the physical security side of things, cables are put through rigorous testing and preparations processes, for example:
- A desktop study followed by a marine survey is used to define the best / safest route for the cable.
- The cable will be specifically manufactured with more or less protection, using an armoured or double armoured cable.
- The cable will be installed as much as possible in defined subsea corridors, officially protected from fishing and anchoring activities, as well as avoiding areas known to be more seismically active. Sections of the cable may also be buried under the seabed (between 1m and 1.5m deep) if and where required.
- On the terrestrial side, cable landing stations are built outside of tsunami zones and in areas with access to redundant power sources and diverse terrestrial fibre networks.
Preventing physical damage prevents cybersecurity problems relating to data loss and breaches, however Hawaiki also has robust reporting and management systems in place to avoid direct breaches to data centers and cable lines.
"Hawaiki has taken care to build a team of experienced network security experts who ensure we're operating to the highest and most up-to-date cybersecurity standards, while providing regular, real-time updates and guidance as the digital landscape evolves," says Galasso.
Hawaiki's Datagrid data center in Invercargill is also an example of the importance of data security in the cable network space. Galasso says flexibility and diversity are paramount.
"Data flows must be safe and secure, regardless of whether you're moving data through submarine cables or ensuring the integrity of data stored in data centers.
"When it comes down to it, countries must have geographic diversity. You don't want to have all your eggs in one basket, an example of which might be, say, storing all of New Zealand's sovereign data in or around Auckland."
Governments and general government security protocol also play a significant role in secure cable networks in Aotearoa. Providers work with many government agencies to abide by strict data security and physical security regulations. Not only does it have to involve our security laws, but it also has to adhere to international laws as well.
"Laying an international submarine cable requires carriers to apply for multiple licenses and permits in all jurisdictions the cable lands in, and, when in operation to comply with local regulations," Galasso remarks.
With a renewed resurgence in submarine cables to help meet demands, Kiwis have every right to be curious about safe communication practices. Galasso says it's important to realise the significance here, and Hawaiki will continue to promote safe cable networks for the benefit of all New Zealanders.
"The New Zealand economy, as well as many aspects of social and community life are now heavily dependent on reliable, secure, high-speed and affordable connectivity to the rest of the world," he says.
"It's incumbent upon operators like Hawaiki to ensure we have the most robust technical processes and modern technology in place to guarantee the highest quality of service.
"It's also important that New Zealand have multiple 'redundant' cables, supported by a vibrant, truly competitive industry that keeps downward pressure on prices; all of which contributes towards growing and protecting a successful digital ecosystem."
So next time you communicate with your friend or business partner on the other side of the world, perhaps it pays to think about that sizeable long structure at the bottom of the ocean and the ways you are being kept safe during your experience.
