ExtraHop Reveal(x) brings cutting-edge AI to network security analytics
ExtraHop, a leader in analytics for security and performance management, has now released Reveal(x), bringing all of the latest threat detection and anomaly reporting technologies to customers worldwide.
ExtraHop Reveal(x) is a purpose-built security analytics solution designed to help security practitioners improve visibility to their critical assets by 40% and cut investigation time from days to seconds.
At the core of Reveal(x) is ExtraHop analytics and machine learning technology that has been honed in the most demanding enterprise environments to deliver complete situational intelligence and to automate threat detection and investigation.
Traditional packet capture solutions rely on post-mortem analysis and workflows measured in days and weeks. They also tend to use flow-based network traffic analysis systems, which only analyse a fraction of the network data. This leads to incomplete insights in the alert queue and security teams face two problems: impractical analytics and junk data.
Those problems are unacceptable, particularly when attack surfaces are expanding and attackers are becoming more sophisticated, says ExtraHop CTO and co-founder Jesse Rothstein.
Lead by customers searching for more sophisticated threat detection, ExtraHop decided to take an innovative approach to network security by utilising wire data to capture a complete set of network data.
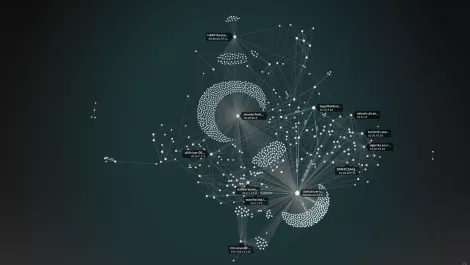
With the complete set of network data, the company then applies machine learning to analyse and correlate behaviour from the application to the device to the infrastructure. The combination wire data and advanced behavioural analytics delivers high fidelity insights in real-time and at scale.

"In security, your intelligence is only as good as the data source from which it's derived," comments 451 Research senior analyst Eric Ogren.
"The network is an ideal place to identify active computing devices and call out threats as they attempt to probe and communicate. ExtraHop Reveal(x) balances real-time critical asset insights with machine learning-based network traffic analytics to create visibility that will help security teams stay one step ahead of security incidents for those assets that matter most."
Reveal(x) delivers situational intelligence and automated investigation that turns the network into the most complete objective source of insight into the threats and vulnerabilities and includes:
Unprecedented Enterprise Visibility: Reveal(x) analyses all network traffic across the entire application payload, identifying in real-time all encrypted traffic, rogue nodes, IoT devices, and BYOD systems. It analyses 40+ protocols, decrypting SSL and perfect forward secrecy (PFS) traffic, and auto-discovers and auto-classifies all connected devices, keeping security teams focused on the most critical assets.
Advanced Behavioural Analytics: Utilising real-time analytics and advanced machine learning, Reveal(x) identifies abnormal behavioural patterns as they occur and correlates them against continuously monitored critical assets so that security teams can target the most immediate threats.
Automated Investigation: The Reveal(x) analytics-first workflow takes you from issue to associated packets in a matter of clicks. This simplicity replaces hours spent manually collecting and parsing through data, enabling real-time insights and rapid root cause determination. Global search and indexing provide immediate access to security insights. And ExtraHop integrates with your existing security infrastructure and automates response using Splunk, Phantom, Palo Alto, ServiceNow, Cisco, Ansible, and others.
ExtraHop Reveal(x) is available now in Singapore, Australia, South Korea, the UK, European Union, and North America via ExtraHop's value-added resellers and for an annual subscription.
For more about ExtraHop Reveal(x) click here or view a demo here.
