Infosec stories - Page 16

HAT to distribute Tufin across Australia & New Zealand
Last month
#
firewalls
#
network infrastructure
#
hybrid cloud
HAT Distribution will distribute Tufin across Australia and New Zealand, targeting complex hybrid networks and regulated sectors.

Give to gain: How sponsoring women strengthens national security
Last month
#
firewalls
#
advanced persistent threat protection
#
breach prevention
Sponsoring women into senior cyber roles is emerging as a strategic lever to plug talent gaps and bolster New Zealand's national security.

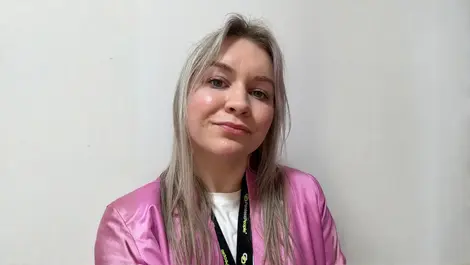
Reversec names Åse Holmberg Zetterlund as Chief Executive
Last month
#
devops
#
partner programmes
#
supply chain
Cyber consultancy Reversec has named former Accenture executive Åse Holmberg Zetterlund as CEO to drive its next phase of global expansion.

Bridging the gap: Cybersecurity breakthroughs and imbalances
Last month
#
data protection
#
endpoint protection
#
mfa
Cybersecurity evolves to AI‑driven defences, but gender imbalances persist, pushing women to fight harder for visibility and leadership.

AI cyber threats outpace staff readiness, report warns
Last month
#
firewalls
#
data protection
#
digital transformation
Attackers' AI use is surging faster than staff skills, Fortinet warns, leaving firms exposed despite rising security awareness spending.

Women redefining emotionally intelligent cyber leadership
Last month
#
digital transformation
#
socs
#
risk & compliance
In cyber security, leaders with self-awareness and emotional intelligence now outperform purely technical experts under relentless pressure.

AI adoption drives security spend but breaches persist
Last month
#
data protection
#
hybrid cloud
#
digital transformation
Rising AI adoption is driving higher security spend, yet most enterprises still suffer repeated breaches as risk outpaces new defences.

Women call for visibility & voice in cybersecurity
Last month
#
risk & compliance
#
cybersecurity
#
recruitment
Women in cybersecurity demand real visibility and inclusion, warning that lack of female voices skews risk, products and leadership decisions.

Microsoft warns of AI agent risks in Cyber Pulse brief
Last month
#
manufacturing
#
digital transformation
#
physical security
Microsoft's new Cyber Pulse briefing warns ungoverned AI agents and 'double agents' pose rising security and compliance risks for firms.

UpGuard unveils Risk Automations to speed cyber fixes
Last month
#
uc
#
siem
#
cloud security
UpGuard debuts Risk Automations to link cyber risk findings with security workflows, promising faster fixes after USD $75 million raise.

Why cybersecurity needs women from non-tech careers
Last month
#
ransomware
#
devops
#
advanced persistent threat protection
Cybersecurity is missing vital human insight; drawing in women and non‑STEM talent could close both the threat and perspective gaps.
HP warns of AI-fuelled 'flat-pack' cyberattacks surge
Last month
#
malware
#
uc
#
phishing
HP reports a surge in AI-powered “flat-pack” cyberattacks as criminals trade sophistication for speed, low cost and mass customisation.

Account Takeover (ATO) fraud: The hidden threat to your business and how to stop it
Last month
#
malware
#
data protection
#
surveillance
Silent account takeover fraud is draining billions as criminals hijack real identities; here's how businesses can finally fight back.
The power of representation in cybersecurity
Last month
#
firewalls
#
devops
#
network security
As cyber threats grow, more women are entering security roles, yet leadership remains male-dominated, risking lost talent and weaker defences.

Flexitech turns to Rimini Street to extend SAP ECC 6
Last month
#
digital transformation
#
cartech
#
it automation
Flexitech shifts SAP ECC 6 support to Rimini Street to cut maintenance costs, extend ERP life and fund security, compliance and R&D plans.

LevelBlue unveils flexible funds-based cyber IR retainer
Last month
#
ransomware
#
devops
#
socs
LevelBlue launches Resilience Retainer, a flexible funds-based cyber incident response service with rapid SLAs and rollover security spend.

Cloudflare flags AI-fuelled identity & SaaS attacks
Last month
#
saas
#
firewalls
#
ddos
Cloudflare warns AI-driven identity fraud and SaaS abuse are reshaping cybercrime, as global costs hit USD $10.5 trillion a year.

AI scales in APAC finance as tokenisation gains pace
Last month
#
digital transformation
#
biometrics
#
fintech
APAC finance firms race to scale AI from pilots to production as tokenisation and blockchain investments signal deeper market overhaul ahead.

Cyber extortion tops 2025 attacks as AI risks escalate
Last month
#
data protection
#
ransomware
#
mfa
Cyber extortion has overtaken email scams as the top 2025 attack, as AI-powered threats grow and financial firms become prime targets.

Netskope, Forescout expand zero trust to all devices
Last month
#
firewalls
#
hyperscale
#
network security
Netskope and Forescout link tools to push zero trust across managed and unmanaged devices, curbing lateral movement on local networks.