All organizations are vulnerable to browser ransomware. Here's why
Ransomware is notoriously known as malware that encrypts files on victim's local machine, before attackers demand payment for restoration. However, with the migration of valuable data to cloud and third-party SaaS applications, attackers no longer need to deliver malware to endpoints. Instead, they've developed numerous, low-effort methods to gain access to sensitive data stored in cloud and SaaS applications through browser-based techniques. Account compromise/takeovers are orchestrated through various means, such as:
- Exploiting vulnerabilities in authentication flows
- Credential-based attacks: Weak passwords, credential reuse, and breached passwords enable attackers to perform credential stuffing and password spraying at scale.
- OAuth and SAML workflow exploits: Many Saas applications have vulnerabilities within their authentication flows. Notably, security researchers at Salt Security, highlighted vulnerabilities in common apps like Grammarly that allowed account takeovers using access tokens from attacker controlled third party applications.
- Third-party application risks
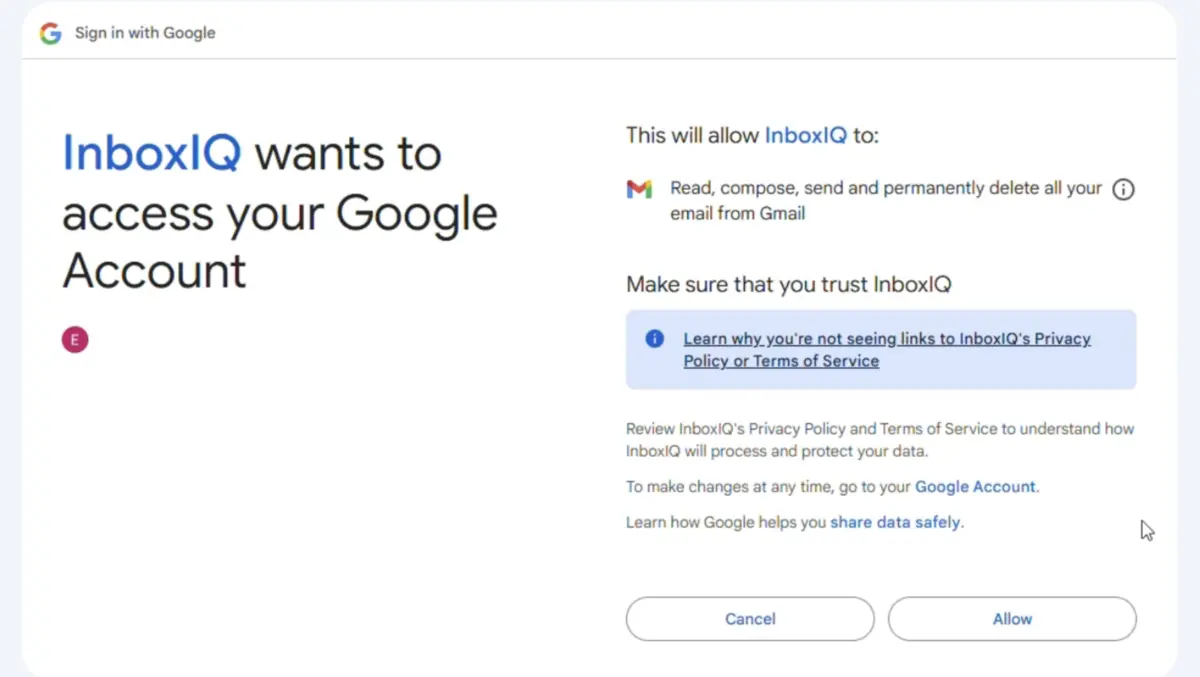
- Leveraging OAuth consent grant: When users grant permission to applications through OAuth consent screens, they provide attackers with persistent access to their accounts. Malicious applications often request excessive permissions that extend beyond their stated functionality. Once granted, these permissions allow attackers to access, modify, and extract sensitive data without additional authentication challenges. The permissions persist until explicitly revoked, creating a long-term vulnerability. (Watch a demo on OAuth Consent-based Browser Ransomware Attack)
- Risky browser extensions: Extensions can exploit authenticated sessions and extract sensitive information. These extensions operate with the same privileges as the browser itself when accessing certain websites. Malicious extensions can silently harvest authentication tokens, manipulate web content, and even initiate transactions without the user's knowledge. (Watch a demo on Gmail Account Hijacking using Browser Extensions)
- Social engineering and advanced phishing
- Brand impersonation campaigns: Attackers create convincing replicas of legitimate websites using typosquatted domains or homograph attacks. These sites are designed to harvest credentials and authentication tokens.
- Browser-in-the-middle attacks: In this technique, victims' entire login processes are proxied through attacker-controlled systems without any visual indicator to the victim. Unlike traditional phishing that simply captures credentials, these attacks intercept the full authentication flow in real-time, allowing attackers to establish parallel authenticated sessions. This technique bypasses multi-factor authentication by relaying the legitimate authentication responses between the victim and the actual service. (Watch a demo on a Browser in the Middle Browser Ransomware Attack)
- Advanced browser tooling attacks: In more sophisticated scenarios, attackers compromise password manager extensions through polymorphic extensions or browser syncjacking. (Watch a demo on Browser Syncjacking Browser Ransomware Attack)
Once attackers gain access to accounts, they can delete data and leave ransom demands. The deletions appear as legitimate user actions from the service provider's perspective. Many SaaS platforms have limited ability to recover from such events, similar to the "permanently delete" commands that require explicit confirmation in services like AWS.
For organizations that rely heavily on Saas services such as enterprise file storage, collaboration platforms, or source code repositories, the business impact of such attacks can be severe. The potential loss of intellectual property, operational data, or customer information creates pressure to pay ransoms. (Watch a demo on Browser Ransomware Attack on Google Drive, deleting even shared drive assets)
Perhaps most concerning is that browser-native ransomware attacks operate outside the detection capabilities of traditional Endpoint Detection and Response (EDR) solutions. Since no malware is downloaded to the endpoint, EDR systems are ineffective against these threat vectors. Standard security tools monitor for file system changes, suspicious processes, or known malware signatures—none of which occur in browser-native attacks that leverage legitimate web protocols and APIs.
No Malware, no detection, no recovery—Browser-native ransomware is the new security nightmare.
When evaluating security posture against ransomware threats, organizations must look beyond endpoint protection to address browser-native attack vectors. The next generation of ransomware protection requires security tools that can monitor browser activity, detect risky OAuth requests, and protect against malicious extensions. With hundreds of potential browser-based entry points, it is apparent that only a browser detection and response solution can protect against browser ransomware.

