
Using layered security to stay safe over the holidays
Tue, 18th Dec 2018
Holidays are a particularly active time for cybercriminals as large volumes of transactions are conducted online.
The days leading up to the festive season are prime time for attackers to build malware, ransomware, and phishing campaigns to prey on holiday shoppers.
SonicWall found that at a macro level, malware attacks dipped in 2018, while ransomware, phishing and cryptojacking attacks all increased significantly.
Over the nine-day Thanksgiving holiday shopping window from November 19 to 27, it found that its customers faced:
- 91 million malware attacks (34% decrease over 2017)
- 889,933 ransomware attacks (432% increase over 2017)
- 45% increase in phishing attacks compared to the average day in 2018
As online shopping becomes increasingly convenient and accessible, more and more consumers are doing their Black Friday shopping online instead of in brick-and-mortar stores.
According to Reuters, online sales surpassed $6 billion on Black Friday in the US — a 23% jump over last year.
At the same time, SonicWall's Capture Labs threat researchers recorded 28 times more ransomware attacks on Black Friday compared to last year.
As cyber criminals become more aggressive, organisations need to seriously consider taking a layered approach to cybersecurity in order to keep themselves safe.
How layered security protects the enterprise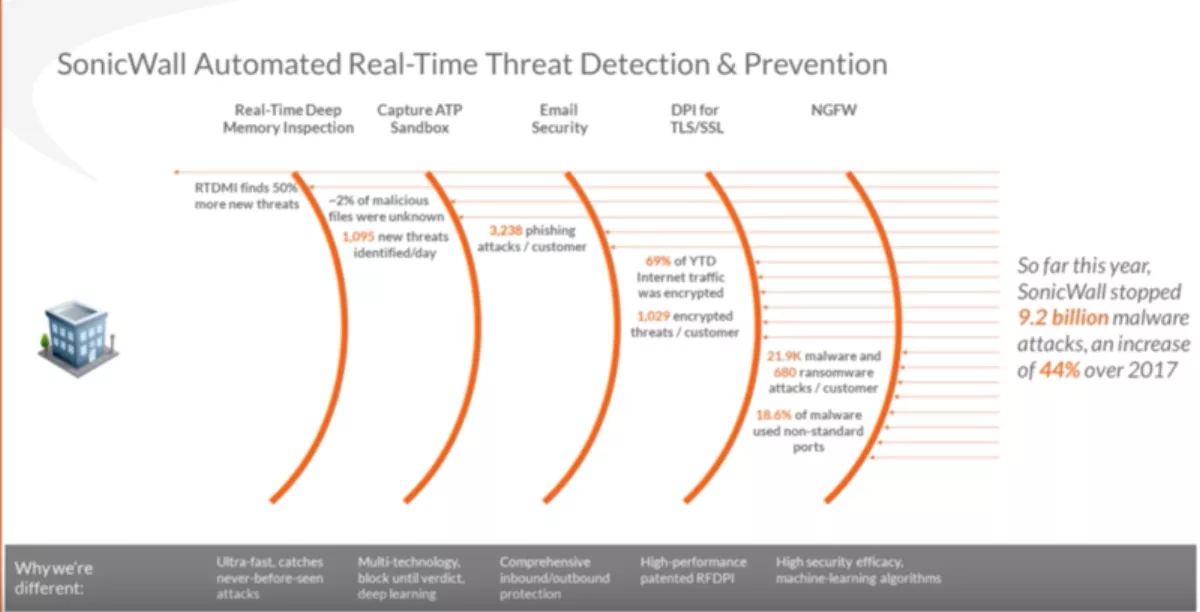
A layered approach means having different levels of security measure that systematically filters out different types of threat as information is accessed by the user
SonicWall CEO Bill Conner and CTO John Gmuender explain how layered security works, from the firewall to real-time deep memory inspection.
Conner says that most of SonicWall's competitors fail on not putting the firewall on non-standard ports which, malware writers take advantage of.
"If your firewall doesn't analyse non-standard ports, it's a huge gap.
He adds that many of them don't turn them on more ports because performance goes down when they do.
DPI-SSL
In 2017, there were over 1000 encrypted threats per SonicWall customer.
The second layer of security is Deep Packet Inspection of Secure Socket Layer (DPI-SSL).
Gmuender says, "If you have a connection using SSL, it's encrypted. If malware is utilising a connection like that, you don't get visibility into the connection without DPI-SSL."
"Nothing else will help if it's still encrypted," Conner adds.
Email Security
Conner says that email is the number one way attackers infiltrate an organisation, with over 3000 phishing attacks being found per customer.
"They come in through either phishing, whale phishing or plain email; through pdfs, and through Microsoft Office applications.
Gmuender adds that SonicWall's email security has integrated capture, meaning all the analysis happens locally in the solution.
Capture ATP Sandbox
The next layer of security is the sandbox.
"Just on the traditional sandbox engine, virtualisation, hypervisor and emulation, we're up to a 1000 threats identified a day, and it's doubled in a year," Conner says.
The sandbox also contains the two percent of malicious files that get through the first three security layers.
Real-time deep memory inspection (RTDMI)
"I've spent a lot of time with governments and enterprises behind the curtain on what this is finding, and there are three key findings," Conner says.
The first finding is that the largest three items, in terms of vulnerabilities that aren't being seen by traditional sandboxing, are Microsoft Office applications, pdfs, and increasingly now, side-channel attacks – such as the fourth iteration of a side-channel on an Intel chip.
"So, you've heard of Meltdown, you've heard of Spectre, you've heard of Foreshadow, the last one just came - RTDMI is going to be the most important thing for small-to-medium businesses, enterprises, governments.
Conner says in the next two years, these unknown malware attacks through pdf, Microsoft Office, and side channels are going to be dramatically increasing, and they're going to be extremely dangerous.
"And that's why we placed this capability behind every solution we have.